Malware ‘Meal Kits’ Are Helping Attackers Steal Businesses’ Lunch, HP Finds
31 Oktober 2023 - 2:00PM

HP Inc. (NYSE: HPQ) today issued its quarterly HP Wolf Security
Threat Insights Report, showing that thriving cybercriminal
marketplaces are offering low-level attackers the tools needed to
bypass detection and infect users.
Based on data from millions of endpoints running HP Wolf
Security, key findings include:
- Houdini’s Last Act: A new campaign targeted
businesses with fake shipping documents concealing Vjw0rm
JavaScript malware. Its obfuscated code allowed the malware to slip
past email defenses and reach endpoints. The analyzed attack
delivered Houdini, a 10-year-old VBScript RAT. This shows that,
with the right pre-packaged tools from cybercrime marketplaces,
hackers can still use vintage malware effectively by abusing the
scripting features built into operating systems.
- Cybercriminals Deploy “Jekyll and Hyde”
Attacks: HP discovered a Parallax RAT campaign launching
two threads when a user opens a malicious scanned invoice designed
to trick users. The “Jekyll” thread opens a decoy invoice copied
from a legitimate online template, reducing suspicion, while the
“Hyde” runs the malware in the background. This attack would be
easy for threat actors to carry out, as pre-packaged Parallax kits
have been advertised on hacking forums for $65 USD per month.
Alex Holland, Senior Malware Analyst in the HP Wolf Security
threat research team, comments:
"Threat actors today can easily purchase pre-packaged,
user-friendly malware ‘meal kits’, that infect systems with a
single click. Instead of creating their own tools, low-level
cybercriminals can access kits that use living-off-the-land
tactics. These stealthy in-memory attacks are often harder to
detect due to security tool exclusions for admin use, like
automation.”
HP also identified attackers are “hazing” aspiring
cybercriminals by hosting fake malware building kits on code
sharing platforms like GitHub. These malicious code repositories
trick wannabe threat actors into infecting their own machines. One
popular malware kit, XWorm, is advertised on underground markets
for as much as $500 USD, driving resource-strapped cybercriminals
to buy fake cracked versions.
By isolating threats that have evaded detection tools on PCs –
but still allowing malware to detonate safely – HP Wolf Security
has specific insight into the latest techniques used by
cybercriminals in the fast-changing cybercrime landscape. To date,
HP Wolf Security customers have clicked on over 30 billion email
attachments, web pages, and downloaded files with no reported
breaches.
The report details how cybercriminals continue to diversify
attack methods to bypass security policies and detection tools.
Other findings include:
- Archives were the most popular malware delivery type for the
sixth quarter running, used in 36% of cases analyzed by HP.
- Despite being disabled by default, macro-enabled Excel add-in
threats (.xlam) rose to the 7th most popular file extension abused
by attackers in Q3, up from 46th place in Q2. Q3 also saw malware
campaigns abusing PowerPoint add-ins.
- At least 12% of email threats identified by HP Sure Click
bypassed one or more email gateway scanner in both Q3, and Q2.
- Q3 saw an increase in attacks using exploits in Excel (91%) and
Word (68%) formats.
- There was a 5%-point rise in PDF threats isolated by HP Wolf
Security compared to Q2.
- The top threat vectors in Q3 were email (80%) and downloads
from browsers (11%).
“While the tools for crafting stealthy attacks are readily
available, threat actors still rely on the user clicking,”
continues Alex Holland. “To neutralize the risk of pre-packaged
malware kits, businesses should isolate high-risk activities, like
opening email attachments, link clicks, and downloads. This
significantly minimizes the potential for a breach by reducing the
attack surface."
HP Wolf Security runs risky tasks in isolated, hardware-enforced
virtual machines running on the endpoint to protect users, without
impacting their productivity. It also captures detailed traces of
attempted infections. HP’s application isolation technology
mitigates threats that slip past other security tools and provides
unique insights into intrusion techniques and threat actor
behavior.
About the data
This data was gathered from consenting HP Wolf Security
customers from July-September 2023.
About HP
HP Inc. (NYSE: HPQ) is a global technology leader and creator of
solutions that enable people to bring their ideas to life and
connect to the things that matter most. Operating in more than 170
countries, HP delivers a wide range of innovative and sustainable
devices, services and subscriptions for personal computing,
printing, 3D printing, hybrid work, gaming, and more. For more
information, please visit: http://www.hp.com.
About HP Wolf Security
HP Wolf Security is a new breed of endpoint security. HP’s
portfolio of hardware-enforced security and endpoint-focused
security services are designed to help organizations safeguard PCs,
printers, and people from circling cyber predators. HP Wolf
Security provides comprehensive endpoint protection and resiliency
that starts at the hardware level and extends across software and
services. Visit https://hp.com/wolf
HP Media Relationsmediarelations@hp.com
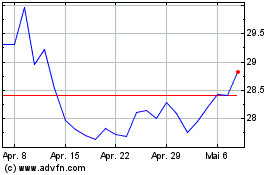
HP (NYSE:HPQ)
Historical Stock Chart
Von Jun 2024 bis Jul 2024
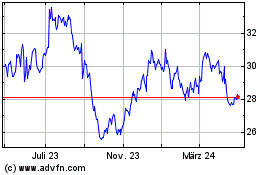
HP (NYSE:HPQ)
Historical Stock Chart
Von Jul 2023 bis Jul 2024