HP Identifies Top Enterprise Security Threats
03 Februar 2014 - 1:45PM
Marketwired
HP Identifies Top Enterprise Security Threats
Annual Report Examines Vulnerability and Threat Landscape,
Provides Actionable Security Intelligence to Protect Attack
Surface
PALO ALTO, CA--(Marketwired - Feb 3, 2014) - HP (NYSE:
HPQ) today published the Cyber Risk Report 2013, identifying
top enterprise security vulnerabilities and providing analysis of
the expanding threat landscape.
Developed by HP Security Research, the annual report provides
in-depth data and analysis around the most pressing security issues
plaguing enterprises. This year's report details factors that
contributed most to the growing attack surface in 2013 -- increased
reliance on mobile devices, proliferation of insecure software and
the growing use of Java -- and outlines recommendations for
organizations to minimize security risk and the overall impact of
attacks.
"Adversaries today are more adept than ever and are
collaborating more effectively to take advantage of vulnerabilities
across an ever-expanding attack surface," said Jacob West, chief
technology officer, Enterprise Security Products, HP. "The industry
must band together to proactively share security intelligence and
tactics in order to disrupt malicious activities driven by the
growing underground marketplace."
Highlights and key findings from the report
- While vulnerability research continued to gain attention, the
total number of publicly disclosed vulnerabilities decreased by 6
percent year over year,(1) and the number of high-severity
vulnerabilities declined for the fourth consecutive year,
decreasing by 9 percent.(1) Although unquantifiable, the decline
may be an indication as to a surge in vulnerabilities that are not
publicly disclosed but rather delivered to the black market for
private and/or nefarious consumption.
- Nearly 80 percent(2) of applications reviewed contained
vulnerabilities rooted outside their source code. Even expertly
coded software can be dangerously vulnerable if misconfigured.
- Inconsistent and varying definitions of "malware" complicate
risk analysis. In an examination of more than 500,000 mobile
applications for Android, HP found major discrepancies between how
antivirus engines and mobile platform vendors classify
malware.(3)
- Forty-six percent(2) of mobile applications studied use
encryption improperly. HP research shows that mobile developers
often fail to use encryption when storing sensitive data on mobile
devices, rely on weak algorithms to do so, or misuse stronger
encryption capabilities, rendering them ineffective.
- Internet Explorer was the software most targeted by HP Zero Day
Initiative (ZDI) vulnerability researchers in 2013, and accounted
for more than 50 percent(4) of vulnerabilities acquired by the
program. This attention results from market forces focusing
researchers on Microsoft vulnerabilities and does not reflect on
the overall security of Internet Explorer.
- Sandbox bypass vulnerabilities were the most prevalent and
damaging for Java users.(2) Adversaries significantly escalated
their exploitation of Java by simultaneously targeting multiple
known (and zero day) vulnerabilities in combined attacks to
compromise specific targets of interest.
Key recommendations
- In today's world of rising cyberattacks and growing demands for
secure software, it is imperative to eliminate opportunities for
unintentionally revealing information that may be beneficial to
attackers.
- Organizations and developers alike must stay cognizant of
security pitfalls in frameworks and other third-party code,
particularly for hybrid mobile development platforms. Robust
security guidelines must be enacted to protect the integrity of
applications and the privacy of users.
- While it is impossible to eliminate the attack surface without
sacrificing functionality, a combination of the right people,
processes and technology does allow organizations to effectively
minimize the vulnerabilities surrounding it and dramatically reduce
overall risk.
- Collaboration and threat intelligence sharing among the
security industry helps gain insight into adversary tactics,
allowing for more proactive defense, strengthened protections
offered in security solutions, and an overall safer
environment.
Methodology HP has published its Cyber Risk Report annually
since 2009. HP Security Research leverages a number of internal and
external sources to develop the report, including the HP Zero Day
Initiative, HP Fortify on Demand security assessments, HP Fortify
Software Security Research, ReversingLabs and the National
Vulnerability Database. The full methodology is detailed in the
report.
Additional information about HP Enterprise Security Products is
available at www.hpenterprisesecurity.com.
HP will be addressing the latest trends in enterprise security
at the RSA Conference 2014, taking place February 24-28 in San
Francisco. Additional information about HP at this year's
conference is available here.
HP's premier Americas client event, HP Discover, takes place
June 10-12 in Las Vegas.
(1) Cyber Risk Report 2013, HP Security Research, February 2014,
p.20-21. (2) Cyber Risk Report 2013, p. 4-5. (3) HP Fortify on
Demand findings included in the Cyber Risk Report 2013, p. 24. (4)
ZDI data included in the Cyber Risk Report 2013, p. 6.
About HP HP creates new possibilities for technology to have a
meaningful impact on people, businesses, governments and
society. With the broadest technology portfolio spanning
printing, personal systems, software, services and IT
infrastructure, HP delivers solutions for customers' most complex
challenges in every region of the world. More information
about HP is available at http://www.hp.com.
Java is a registered trademark of Oracle and/or its affiliates.
Microsoft is a U.S. registered trademark of the Microsoft group of
companies.
This news release contains forward-looking statements that
involve risks, uncertainties and assumptions. If such risks or
uncertainties materialize or such assumptions prove incorrect, the
results of HP and its consolidated subsidiaries could differ
materially from those expressed or implied by such forward-looking
statements and assumptions. All statements other than statements of
historical fact are statements that could be deemed forward-looking
statements, including but not limited to statements of the plans,
strategies and objectives of management for future operations; any
statements concerning expected development, performance, market
share or competitive performance relating to products and services;
any statements regarding anticipated operational and financial
results; any statements of expectation or belief; and any
statements of assumptions underlying any of the foregoing. Risks,
uncertainties and assumptions include the need to address the many
challenges facing HP's businesses; the competitive pressures faced
by HP's businesses; risks associated with executing HP's strategy
and plans for future operations; the impact of macroeconomic and
geopolitical trends and events; the need to manage third-party
suppliers and the distribution of HP's products and services
effectively; the protection of HP's intellectual property assets,
including intellectual property licensed from third parties; risks
associated with HP's international operations; the development and
transition of new products and services and the enhancement of
existing products and services to meet customer needs and respond
to emerging technological trends; the execution and performance of
contracts by HP and its suppliers, customers, clients and partners;
the hiring and retention of key employees; integration and other
risks associated with business combination and investment
transactions; the execution, timing and results of restructuring
plans, including estimates and assumptions related to the cost and
the anticipated benefits of implementing those plans; the
resolution of pending investigations, claims and disputes; and
other risks that are described in HP's Annual Report on Form 10-K
for the fiscal year ended October 31, 2013, and that are otherwise
described or updated from time to time in HP's Securities and
Exchange Commission reports. HP assumes no obligation and does not
intend to update these forward-looking statements.
© 2014 Hewlett-Packard Development Company, L.P. The information
contained herein is subject to change without notice. The only
warranties for HP products and services are set forth in the
express warranty statements accompanying such products and
services. Nothing herein should be construed as constituting an
additional warranty. HP shall not be liable for technical or
editorial errors or omissions contained herein.
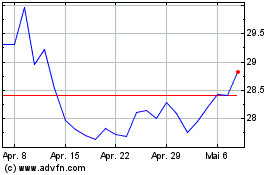
HP (NYSE:HPQ)
Historical Stock Chart
Von Jun 2024 bis Jul 2024
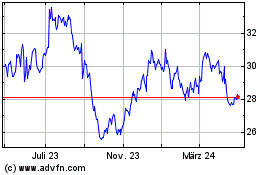
HP (NYSE:HPQ)
Historical Stock Chart
Von Jul 2023 bis Jul 2024